Security Maturity on TEC37
Join host Robb Boyd as he speaks with WWT's Jill Cochrane, Kris Carr, and Geoff Hancock, as they walk through different levels of cybersecurity maturity to give CISOs, CEOs and CIOs the confidence to improve their security postures wisely and maximize resources.

Incredible conversation with three security experts from World Wide Technology. Jill Cochrane, Kris Carr, and Geoff Hancock.
A few snippets from the show...
(registration required).
I had the pleasure of leading a discussion among these three experts who had collaborated on an extremely helpful white paper:

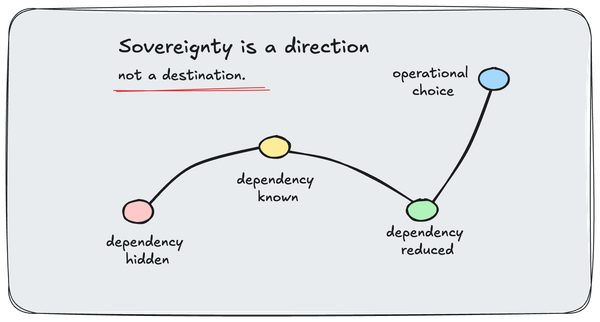
We discuss how to identify gaps and create a strategic roadmap to continued maturity. A model that helps you better understand the reality of where your organization stands today and the steps you should take to level up.
The five stage are:
- Level 1 – Ad-hoc and initial
- Level 2 – Established and current security
- Level 3 – Defined and approved security
- Level 4 – Actively managed security
- Level 5 – Optimized and innovating security